Criminals gain control over Mac with BackDoor.Olyx
June 22, 2011
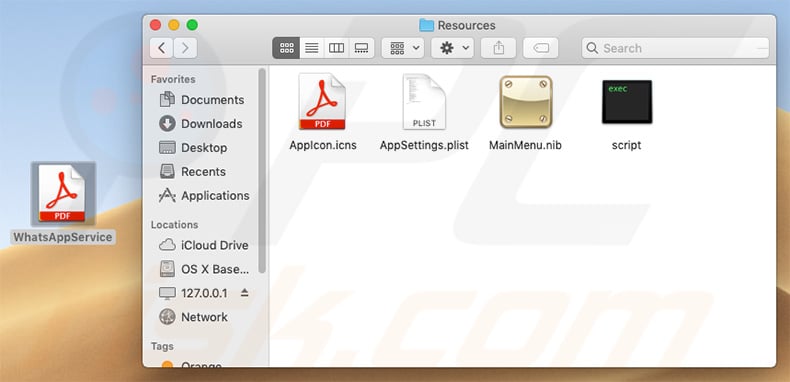
May 09, 2007 I just recently started my own business and part of my services also involves fixing computers with Mac OS X on it, so I'm wanting to learn more about Mac OS X in depth. In windows theres a 'backdoor' sort of speak called registry editor and its hard to explain what does but it sort of puts windows and program settings all in one screen. A new piece of malware targeting Macs was discovered this week. It's called Backdoor.MAC.Eleanor and here's everything you need to know about it and keeping your Mac safe.
Doctor Web—the leading Russian developer of anti-virus software —informs users that its virus analysts have discovered a new threat to computers running Mac OS X. BackDoor.Olyx is the second known backdoor for the operating system. If a machine is compromised by the malware, attackers get an opportunity to covertly control the computer. The backdoor receives commands from a remote server to create, transfer, rename, delete various files, as well as some other instructions.
The number of malicious programs for MAC OS X is small, especially compared with the number of threats to Windows. Until recently only one backdoor program for the OS was known—BackDoor.DarkHole. Versions of this malware exist for Mac OS X and for Windows. When launched, it enables hackers to open web pages in the default browser on the infected machine, restart the computer remotely and perform various operations with files. Now, in the Dr.Web virus database contains entries for both BackDoor.DarkHole and BackDoor.Olyx.
The program gets to a user's computer as an application designed for Macs featuring the Intel-compatible architecture, BackDoor.Olyx creates the /Library/Application Support/google/ directory on the disk to which it saves a file named startp. Then BackDoor.Olyx places the file /Library/ LaunchAgents/www.google.com.tstart.plist into the home directory, and uses the file to launch the malicious object after a system reboot.
After that the program moves itself to a temporary folder named google.tmp to delete the executable from its original location. As the name implies, BackDoor.Olyx operates in an infected system as a backdoor which includes downloading and running malicious files on infected machines and executing various commands in the /bin/bash shell. Thus, attackers can gain control over an infected computer without the user's knowledge.
Users of Dr.Web for Mac OS X can rest assured about the security of their computers, since the signature of the malware has already been added to the Dr.Web virus database. To prevent BackDoor.Olyx from infecting systems, users of Dr.Web for Mac OS X are recommended to enable automatic updating and scan their hard drives regularly.
Tell us what you think
You will be awarded one Dr.Webling per comment. To ask Doctor Web's site administration about a news item, enter @admin at the beginning of your comment. If your question is for the author of one of the comments, put @ before their names.
Other comments
Classification
Malware
Backdoor
OSX
Backdoor:OSX/MacKontrol.A
Summary

Backdoor:OSX/MacKontrol.A connects to a remote server to receive further instructions, without the knowledge or permission from the user.

Removal
Automatic action
Backdoor For Mac Catalina
The F-Secure security product will automatically remove the file.
Manual removal
- Open Activity Monitor, select launched, and click Quit Process.
- Open Terminal, then execute the following:
- rm /Library/launched
- rm ~/Library/LaunchAgents/com.apple.FolderActionsxl.plist
Suspect a file is incorrectly detected (a False Positive)?
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First check if your F-Secure security program is using the latest detection database updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
NOTE If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note You need administrative rights to change the settings.
For more Support
User Guide
See the user guide for your product on the Help Center.
Contact Support
Chat with or call an expert for help.
Submit a sample
Submit a file or URL for further analysis.
Backdoor For Facebook Log In
Technical Details
Arrival
MacKontrol.A is dropped into the system by malicious Word documents that exploit the vulnerability identified by CVE-2009-0563.

Backdoor:OSX/MacKontrol.A connects to a remote server to receive further instructions, without the knowledge or permission from the user.
Removal
Automatic action
Backdoor For Mac Catalina
The F-Secure security product will automatically remove the file.
Manual removal
- Open Activity Monitor, select launched, and click Quit Process.
- Open Terminal, then execute the following:
- rm /Library/launched
- rm ~/Library/LaunchAgents/com.apple.FolderActionsxl.plist
Suspect a file is incorrectly detected (a False Positive)?
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
Check for the latest database updates
First check if your F-Secure security program is using the latest detection database updates, then try scanning the file again.
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
NOTE If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note You need administrative rights to change the settings.
For more Support
User Guide
See the user guide for your product on the Help Center.
Contact Support
Chat with or call an expert for help.
Submit a sample
Submit a file or URL for further analysis.
Backdoor For Facebook Log In
Technical Details
Arrival
MacKontrol.A is dropped into the system by malicious Word documents that exploit the vulnerability identified by CVE-2009-0563.
Installation
The malware drops the following copy of itself:
- /Library/launched
It creates the following launchpoint for the file above:
- ~/Library/LaunchAgents/com.apple.FolderActionsxl.plist
Payload
The malware connects tofreetibet2012[...].xicp.com[...] to obtain additional commands.
Macy's Backdoor
It is capable of performing the following actions:
Backdoor For Mac App
- Deleting files
- Terminating processes
- Getting system info, such as system version, username, hostname, etc.
- Getting process lists
- Opening remote shell
- Listing files
- Uploading, downloading and executing files
- Removing launchpoint
